News & Events
Syslog-ng 101, part 7: Networking
This is the seventh part of my syslog-ng tutorial. Last time, we learned about syslog-ng destinations and the log path. Today, we learn about syslog-ng network logging. At the end of the session, we will send test messages to a syslog-ng network source.
Security Awareness Training ROI: Part 2 Of 3
If you haven’t read Part 1 of our Security Awareness Training ROI, you can here. In it, we discussed the high-level overview of why security awareness training should be a vital part of any company’s cybersecurity strategy and how to get the best security awareness training ROI.
Open-Source SSH: When Free Is Not Free
Free software, also known as open-source software, sounds like a good way to cut already high IT costs. As the name suggests, it’s free, thus it shouldn’t cost anything. But is it really that simple? Let’s find out.
Active Directory Cyber Resiliency
Reduce Cyber Risk for your organization
In 2021, 25 billion attacks on Azure AD accounts were reported. Your organization Active Directory (AD) security sits as your organization’s cornerstone, but it’s also every cyber villain’s favorite target whom can control your AD and then your entire enterprise.
Syslog-ng 101, part 6: Destinations and log path
This is the sixth part of my syslog-ng tutorial. Last time, we learned about syslog-ng source definitions and how to check the syslog-ng version. Today, we learn about syslog-ng destinations and the log path. At the end of the session, we will also perform a quick syntax check.
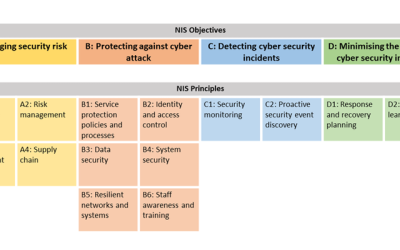
Attackers keep trying, but NCSC’s CAF guidance will keep Active Directory protected
As an IT professional, it shouldn’t surprise you to know that there are 95 million attempted Active Directory (AD) attacks every day. But cyberattack concerns aren’t limited to on-premises Active Directory. In fact, last year, there were more than 25 billion attacks in Azure AD.
White Paper: How to configure syslog-ng™ PE to cooperate with Splunk
Splunk is a popular search and analysis platform. Many users of Splunk also have syslog-ng™ deployed in their environments. This guideline describes scenarios in which Splunk users can benefit from syslog-ng™ Premium Edition features and offers some technical guidance to optimize the syslog-ng™ configuration.
Security Awareness Training ROI: Part 1 Of 3
Today, data breaches and cyber-attacks are becoming so frequent that they aren’t a matter of “if” but “when,” making cybersecurity employee training a must.
SSH in the World of Post-Quantum Cryptography (PQC)
Nowadays, advances in quantum computing are moving at a neck-breaking pace. Giants in the field have been faithfully executing roadmaps and delivering on milestones laid out several years ago. And while it is hard to predict when the advances will reach their breaking point, the threat to classical, public key cryptography is getting closer.
Yubico Channel Awards 2022
Quote from Yubico:
‘‘Congratulations on the award! Thank you for your partnership over the last several years, we are looking forward to many more joint successes!”
“Congratulations Team DTA! It is our pleasure working and growing with your Team.”
About Us
From hardware appliances to software solutions and training, DT Asia understands cybersecurity challenges and can deliver solutions that help detect & identify, protect & secure, authenticate & authorise, and degauss & destroy.
Contact Us
Address
#02-72 WCEGA Tower,
Singapore 658065