Data is one of the most valuable assets that an organization owns. In today’s world, data increasing value comes the need for greater responsibility for data privacy and security. Data breaches, legal and financial penalties, and reputational damage are disastrous consequences for improper handling of sensitive data. Meanwhile government agencies and industry segments are stipulating the proper handling of data such as Singapore PDPA (Personal Data Protection Act 2012) and Banking Act.
In this article, we will discuss different data destruction methods that are in compliance with global data privacy regulations, explain how data is securely erased in HDD and SSDs, and the features and benefits of Secure Data Erasure method. That is, ensure that data is protected at the end of the IT Asset lifecycle where secure data erasure software solution helps organizations erase data securely and comply with regulations.
Different Data Destruction Methods
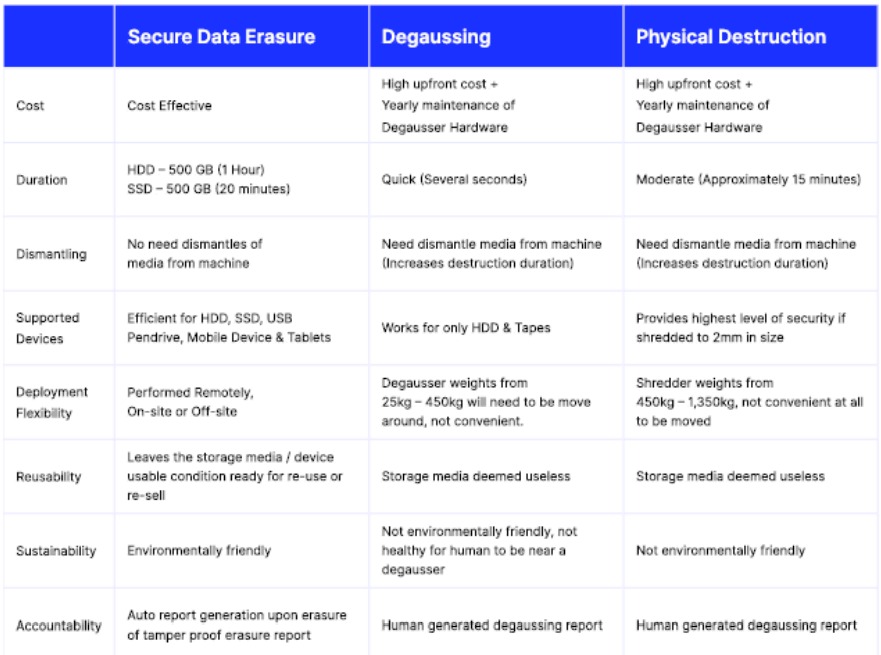
So, what are the different data destruction method? The 3 main methods of data destruction are Data Erasure, Shredding and Degaussing. There is no one method that fits for all, and according to the issued Guidelines for Media Sanitization of The National Institute of Standards and Technology of the United States (NIST), all the 3 data destruction methods will be used based on the data classification and the data sensitivity.
Data Erasure of HDD and SSD uses certified software to destroy data, permanently and irreversibly deleting data from a storage device, such as computer, mobile device or USB Drives. The other two methods are Shredding and Degaussing using physical destruction of particular composite type devices. Shredding of solid-state drive (SSD) is the physical cutting to scrap the SSD storage device. Though effective, but also be risky and environmentally damaging. Risky in sense that there is no software generated tamper evident destruction report hence increasing the risk of inaccurate info which is susceptible to human error. Degaussing of hard disk drives (HDD) works by exposing the drive to strong magnetic field that disrupts the magnetic particles that store data on the disk. The trend is HDD no longer the standard storage type in almost all IT devices today.
Proper data erasure is demanded by many global data privacy regulations, such as the General Data Protection Regulation (GDPR), and those in ASEAN are Singapore (PDPA), Malaysia (PDPA), Indonesia (PDP), Philippines (DPA), Thailand (PDPA) and recently Vietnam (PDPA). In fact, as of January 2023, there are over 120 jurisdictions that have a data privacy law in place. These regulations require organizations to implement appropriate measures to protect the privacy of personal data, including erasing data securely when it is no longer needed. When these devices are no longer in use, failing to properly erase data can lead to serious consequences, including data breaches, identity theft, financial loss, and reputational damage.
Mechanism in Secure Data Erasure of HDD and SSD.
Unfortunately, many organizations still rely on improper methods of data destruction such as simply format a hard drive or a delete files, thinking that this is enough to erase the data. However, these methods only delete the file references and not the actual data, which makes data recovery possible
by someone with the right tools and knowledge. Therefore, the crucial aspect of data handling is Secure Data Erasure. This method involves overwriting the entire drive with industry erasure algorithm, making it impossible to access any previous data stored on the drive. The software can be used to overwrite the entire drive, HDD and SSD, multiple times to ensure that all data is properly erased.
For HDDs, secure data erasure software overwrites the drive multiple times with random data, making it impossible to recover any previous data stored on the drive. This process is known as the Gutmann method and involves overwriting the drive 35 times with different patterns of data. Other erasure algorithm is the NIST Clear (1 Overwriting), NIST Purge (1 Overwriting + 1 Firmware based), DoD 5220.22-M E (3 Overwriting) and so on.
For SSDs, secure data erasure software uses a different process known as the ATA Secure Erase command. The command sends a signal to the drive to erase all data stored on it, including any data that may be in areas that are not easily accessible. This method is effective for SSDs because it specifically targets the flash memory cells where data is stored, ensuring that all data is properly erased.
Features and Benefits of an excellent Secure Data Erasure Software Solution
A secure data erasure software solution is designed to help organizations securely erase data at the end of the IT Asset lifecycle while complying with global data privacy regulations. The key requirement is to be recognized and certified by the in-country authority such as Cyber Security Agency of Singapore (CSA) under the Common Criteria scheme. This certification ensures that the software solution meets stringent security standards and is recognized by many developed and
developing countries that participate in the Common Criteria Recognition Arrangement (CCRA) which allows software solution to be utilized at government level. Other certifications are ADISA, BSIFederal Office for Information security and Attingo shows no data on the media after a forensic data recovery on erased SSD.
Secure data erasure software solution is a comprehensive and user-friendly solution that offers features including the following: 1) Data Security: By using advanced data erasure algorithms, permanently and irreversibly erases data from storage devices, making it impossible to recover even with sophisticated data recovery tools. This ensures that sensitive data remains secure and confidential, protecting organizations from data breaches and cyber-attacks. 2) Cost Savings: By securely erasing data at the end of the IT Asset lifecycle, organizations can avoid costly data breaches and regulatory fines. Additionally, its user-friendly interface and ability to erase data remotely can help organizations save time and resources. 3) Comprehensive Solution: By offering multiple data erasure methods and generating detailed erasure reports. It can be used on a wide range of storage devices such as Laptop, Desktop, Server, Storage, Loose HDD/SSD, USB storage devices & Mobile Device (iOS & Android) and can be used on-site, off-site or remotely, providing flexibility for organizations with varying needs. The detailed erasure reports provide a comprehensive and auditable record of the erasure process, ensuring that organizations can demonstrate compliance to internal and external stakeholders. 4) Environmental Responsibility: By securely erasing data and properly disposing of IT Assets, organizations can reduce their environmental impact and promote sustainability. The software solution helps organizations comply with e-waste regulations by providing detailed erasure reports and chain of custody documentation. On top of that, upon secure data erasure the reusability of the media allows organization to re-use, donate, or re-sell the media or devices.
With the ever-increasing amount of sensitive data being generated and stored on electronic devices, the need to protect sensitive information from falling into the wrong hands avoid the risk of data breaches and regulatory fines. With Secure Data Erasure, not only organizations can have peace of mind knowing that their data is being securely erased and that they are complying with all relevant data privacy regulations, but also saving cost and contributing to the green environment.
Adapted from Securaze whitepaper: Protecting Sensitive Information at the End of the IT Asset Lifecycle – Discussing the Importance of Secure Erasure.
About DT Asia
DT Asia began in 2007 with a clear mission to build the market entry for various pioneering IT security solutions from the US, Europe and Israel.
Today, DT Asia is a regional, value-added distributor of cybersecurity solutions providing cutting-edge technologies to key government organisations and top private sector clients including global banks and Fortune 500 companies. We have offices and partners around the Asia Pacific to better understand the markets and deliver localised solutions.










