A recent incident involving a famous singer has left fans shocked and served as a powerful reminder to industry professionals about the vulnerability of sensitive data—even at the highest levels of production. Known for maintaining strict secrecy around upcoming releases, the artist now faces a serious risk of leaks after unreleased music was stolen.
From Manual Overhead to Operational Advantage: Why Your YubiKey Deployment Needs a CMS
Deploying hardware security keys like YubiKeys is one of the most effective ways to prevent phishing and credential-based attacks. Yet for many IT teams, the initial promise of stronger, phishing-resistant security is often offset by the operational burden that comes with managing these devices at scale.
AI-driven data modeling has arrived
Every data architect knows the struggle. Data modeling often begins with a blank canvas, vague requirements and countless hours spent translating business concepts into structured models for each new project. Meanwhile, your team is under constant pressure to deliver production-ready models faster than ever — yet manual processes continue to slow everything down.
Fake Video Meeting Invites Trick Users Into Installing RMM Tools
Threat actors are leveraging fake meeting invitations for Zoom, Microsoft Teams, Google Meet, and other video conferencing platforms to trick users into installing remote monitoring and management (RMM) tools, according to researchers at Netskope.
5 authentication trends that will define 2026: Authsignal founder’s perspective
As we move into 2026, I’ve been reflecting on where authentication and digital identity are heading. The past year brought meaningful progress: passkeys gained real traction, government-backed digital ID programs launched across multiple regions, and AI agents began reshaping how we think about machine-to-machine trust. In 2026, these trends won’t just continue — they’ll accelerate and fundamentally influence how we design authentication systems.
Running AI Locally? A Used Mac Mini Might Be All You Need
If you’ve been keeping an eye on the latest conversations coming out of Silicon Valley and the broader AI community, you’ve probably noticed a growing trend: developers are buying Mac Mini units to run local AI agents such as the project formerly known as Clawdbot—now rebranded as Moltbot.
OneIAM – A Flexible Solution for Modern Identity and Access Management
As organizations grow, their IT infrastructures often become fragmented — especially when merging with other companies, onboarding new business units, or managing separate identity systems across departments. This fragmentation can make identity and access management (IAM) inefficient, risky, and difficult to administer. RCDevs introduces OneIAM, a flexible approach that simplifies and centralizes IAM across diverse systems without forcing a full migration into a single platform.
Securing AD/LDAP Environments: How OpenOTP Leads the Way
Many European organizations face a distinct challenge: strengthening cybersecurity while complying with strict regulatory frameworks. Across industries such as banking, insurance, education, healthcare, and government, Active Directory (AD) and Lightweight Directory Access Protocol (LDAP) remain fundamental components of IT infrastructure. However, as cyber threats grow increasingly sophisticated and compliance obligations intensify, these organizations must adopt new approaches to secure their AD/LDAP environments without sacrificing operational efficiency or data sovereignty.
Sentinel: Reduce costs with syslog-ng
Organizations adopting Microsoft Sentinel have reported a 93% reduction in time required to configure and deploy new connections, with the time saved in configuration alone valued at $618,000. These gains highlight Sentinel’s flexibility and scalability. However, Sentinel’s consumption-based licensing model introduces a critical challenge: as more systems and data sources are onboarded, costs can grow rapidly, often resulting in unexpected invoice increases.
Top 7 Advantages of Passwordless Authentication for Businesses
The digital landscape continues to evolve rapidly, and so do the methods used to protect online environments. Passwordless authentication has emerged as a powerful alternative to traditional password-based security, helping organizations improve protection while simplifying access. Instead of relying on memorized passwords, users verify their identity through more secure and convenient methods.
From blueprint to business value: How to build an AI-ready data foundation
You already know the stakes.
Nearly 80% of AI initiatives fail, and the root cause is rarely the algorithms—it’s data. You’ve seen how traditional governance slows innovation, creating a trust paradox where controls increase friction instead of confidence. You understand the promise of govern-as-you-go and how quickly organizations can transform when governance becomes embedded rather than enforced.
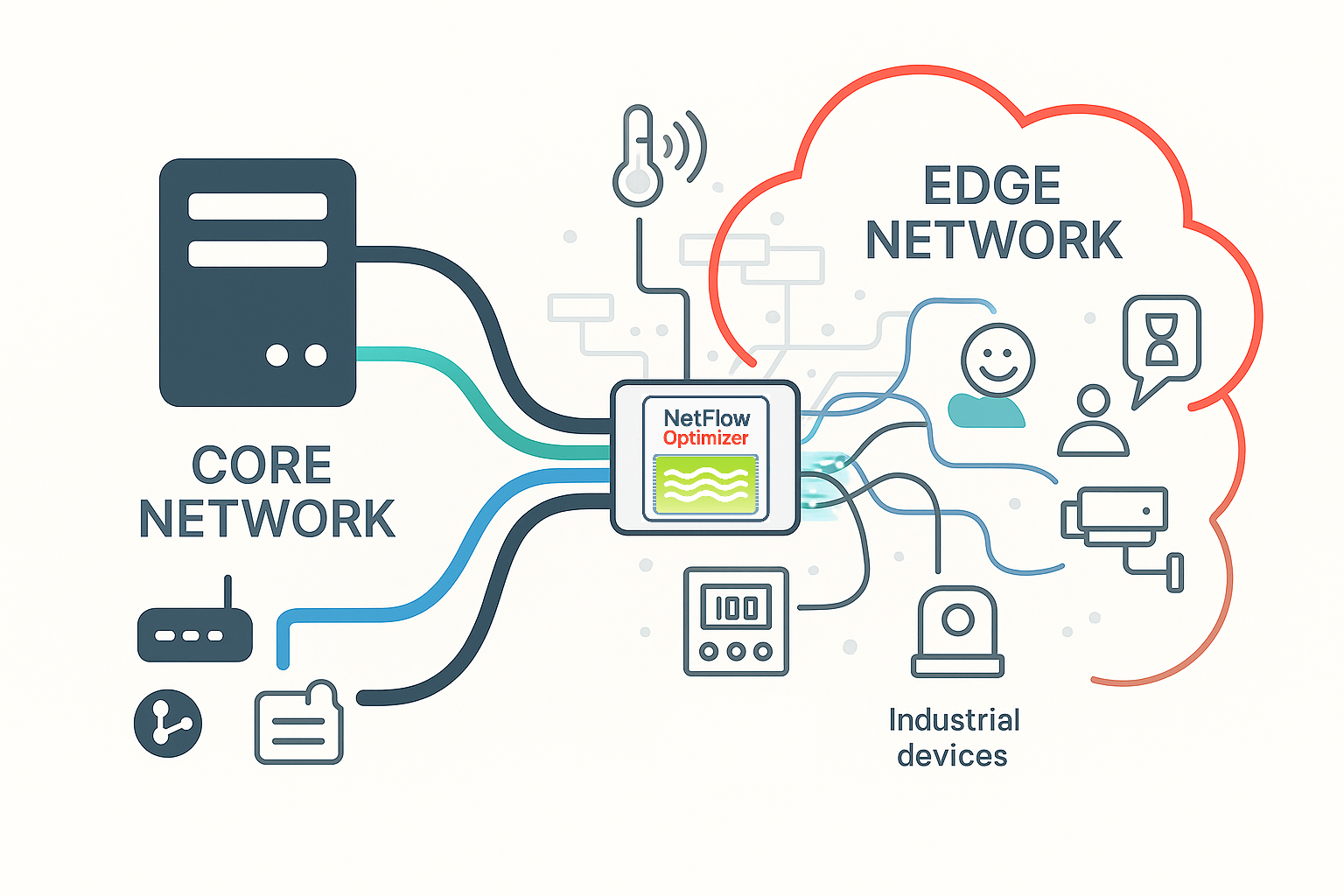
Securing the Edge: How Optimized NetFlow Solves the Visibility Problem for IoT and Industrial Networks
The modern enterprise extends far beyond the traditional data center and the employee laptop. Today’s environments include a vast array of devices operating at the network edge—ranging from smart surveillance cameras and HVAC sensors to specialized Operational Technology (OT) controllers in factories and warehouses. While this growing ecosystem of Internet of Things (IoT) and Industrial Control Systems (ICS) significantly enhances business capabilities, it also introduces a substantial and often overlooked security gap.