Dec 2, 2024 | Uncategorized
Operational Technology (OT) security is a multifaceted challenge, requiring organizations to address diverse risks and vulnerabilities. Frameworks like the NIST Cybersecurity Framework 2.0 (CSF 2.0) help structure these efforts. Although not OT-specific, CSF 2.0...
Nov 26, 2024 | Uncategorized
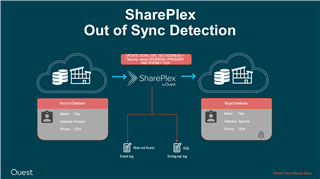
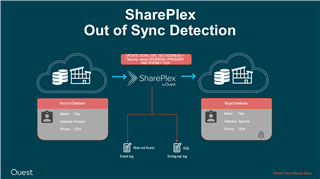
Introduction SharePlex users often inquire about how the tool detects, processes, and resolves discrepancies between rows in source and target databases. SharePlex is specifically designed to maintain synchronization in replication streams, addressing cases where the...
Nov 7, 2024 | Uncategorized
It’s no coincidence that Graylog 6.1 is making its debut right before Halloween. This release is a true powerhouse, designed to address some of the most enduring and complex challenges in Security Information and Event Management (SIEM). With a suite of innovative...

Nov 5, 2024 | Articles, Articles, Articles, Articles
As ransomware attacks surge in sophistication and frequency, businesses and organizations of all sizes face heightened risks. These attacks disrupt operations, lead to significant financial losses, and can irreparably damage reputations. Over the past decade,...