Nov 9, 2023
While the tech world was looking forward to the upcoming release of the iPhone 15 in September, an exciting development is taking place in the market which could have a major impact on those consumers who are seeking almost-current smartphones at lower prices. The...
Oct 25, 2023
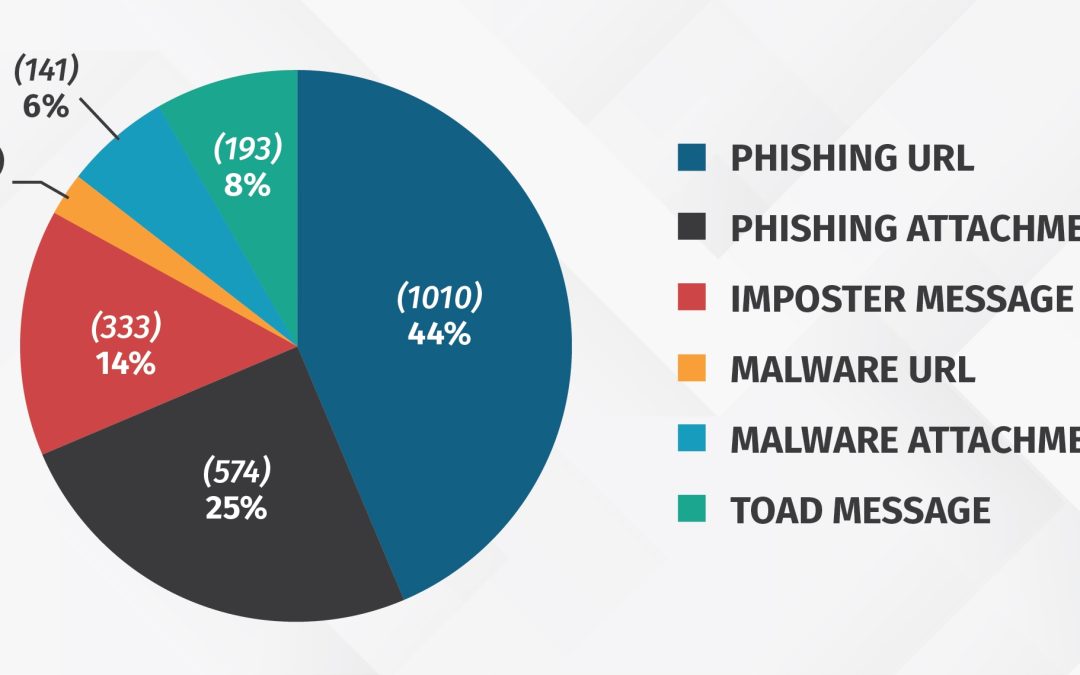
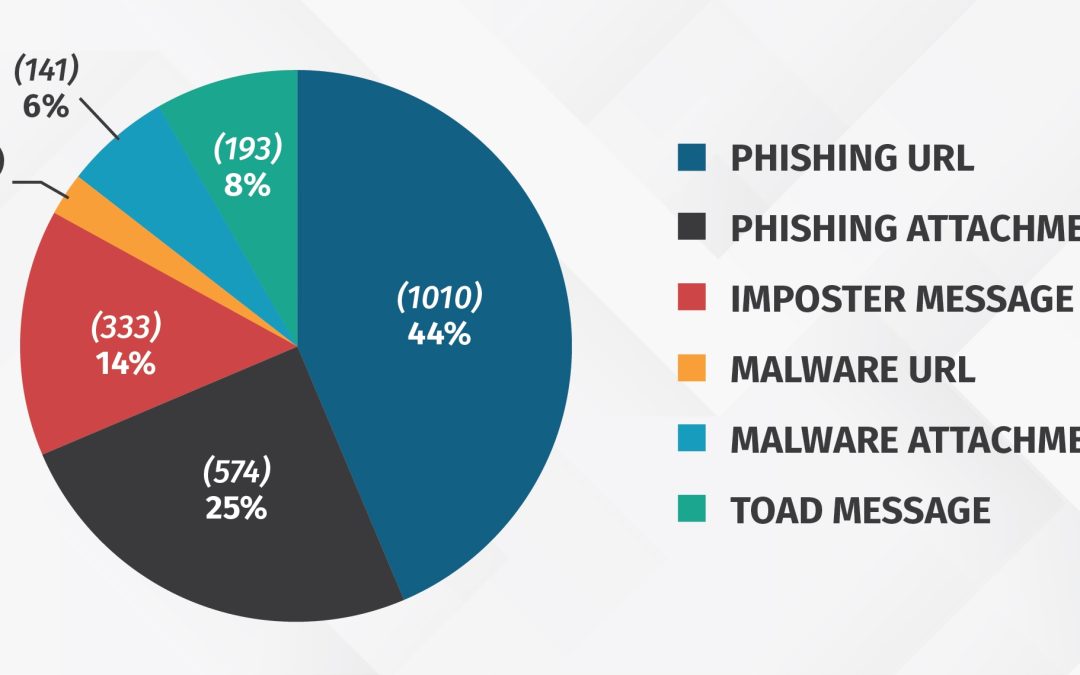
Phishing has been and continues to be one of the most common methods (TTPs) cyber attackers use because it is so effective. Phishing is a simple attack vector that enables cyber attackers to easily scale their attacks, customize for their intended targets, and bypass...

Oct 25, 2023
Threat hunting is proactively identifying and thwarting unusual network activity that could indicate an attempted security breach. It’s a historically manual activity, making it time-intensive and arduous. It’s no wonder, then, why most organizations don’t have the...
Oct 25, 2023
Tenant-to-tenant migrations are increasingly common. Some are necessitated by business changes like mergers, acquisitions, and divestitures, while others are driven by the desire to clean up or consolidate the IT infrastructure to facilitate business processes and...

Oct 23, 2023
Getting data to Splunk can be challenging. Syslog is still the most important data source, and it can provide you with hard-to-solve problems (for example, like high volume, non-compliant messages, unreliable network protocol (UDP), and more). The syslog-ng Premium...