Jun 27, 2023
Helsinki, Finland – June 6, 2023 – To resolve various customer support problems regarding OpenSSH implementations, SSH has launched a support service for OpenSSH. As a result, customers benefit from high-quality SSH support services also for the open-source...

Jun 6, 2023
Do your customers request proof of where their devices have been erased? Do they want confirmation that their devices and confidential data have not left the country or ended up in the wrong hands? Are they looking for proof that all aspects of your contract have been...

Jun 6, 2023
Taking the right steps to secure your Active Directory (AD) has never been more important. Because AD controls who can get into your network and what they can do once they’re inside, failure to implement proper controls will dramatically increase your risk of costly...

May 30, 2023
This is the eighth part of my syslog-ng tutorial. Last time, we learned about network logging. Today, we learn about syslog-ng macros and templates. At the end of the session, we will know how to do a simple log rotation using macros. You can watch the video or read...
May 24, 2023
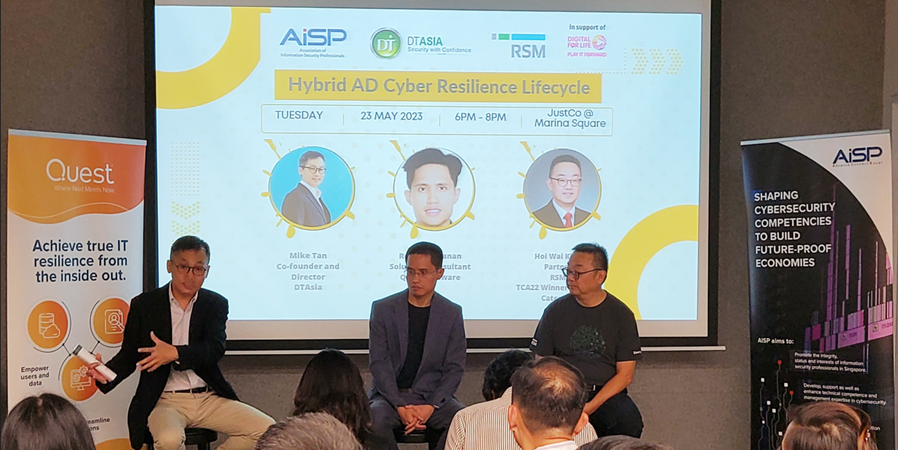
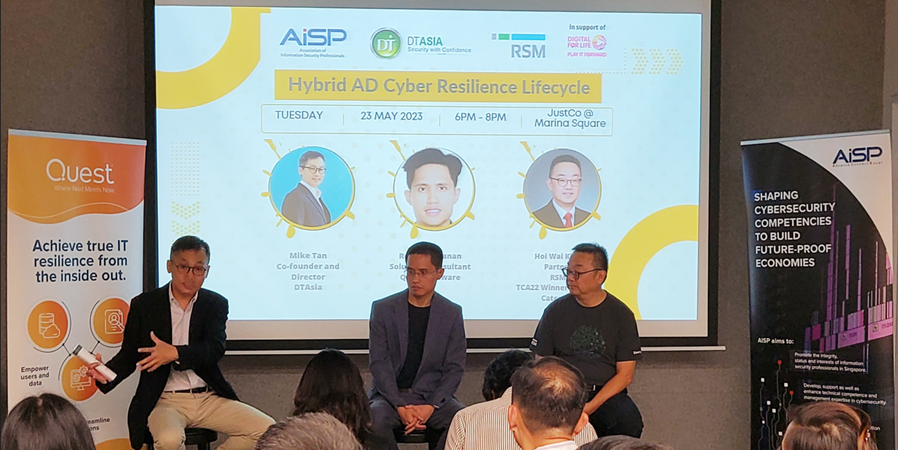
We had a great collaboration with — AiSP, RSM and Quest – on “Hybrid AD Cyber Resilience Lifecycle” and our combined efforts led to a successful panel engagement with the attendees, on 23 May.