Mar 28, 2023 | Uncategorized
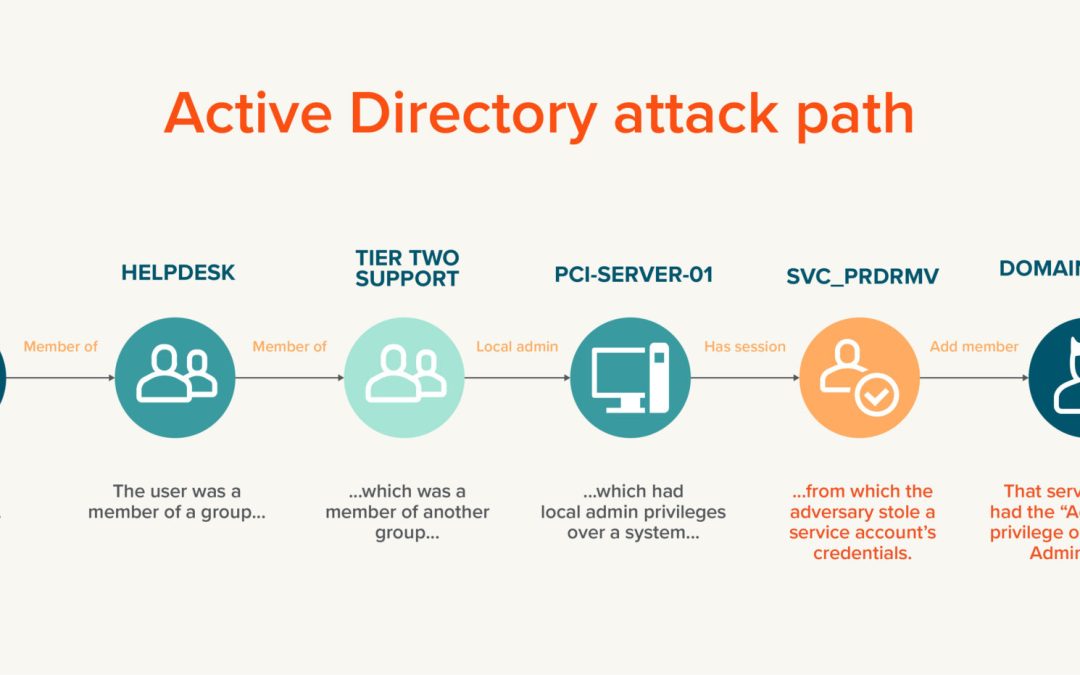
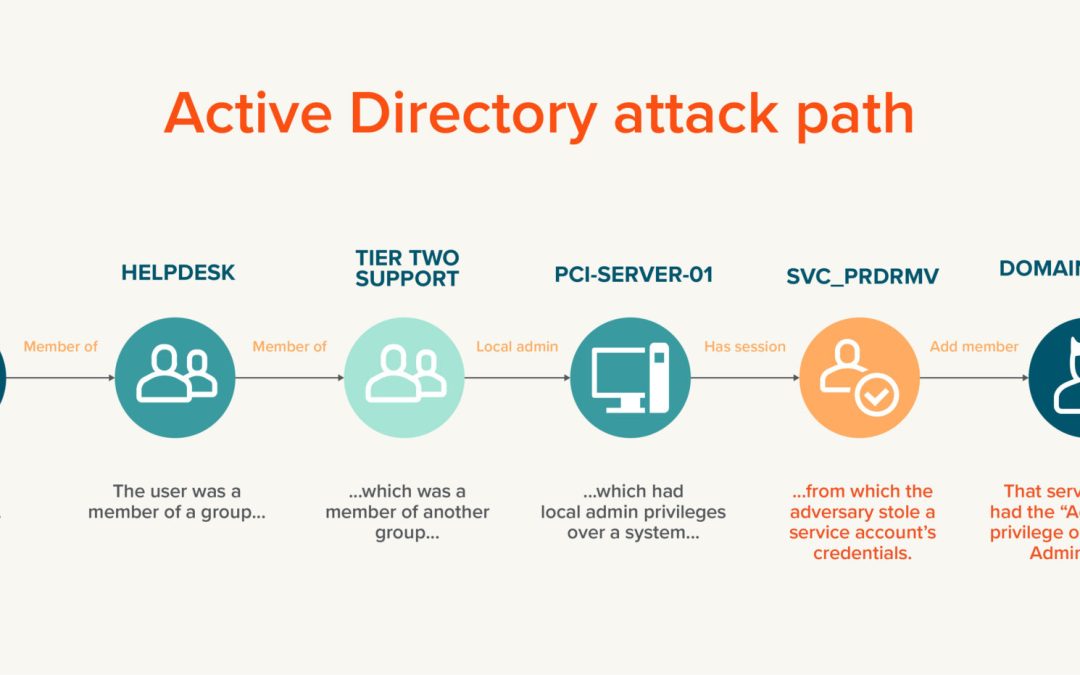
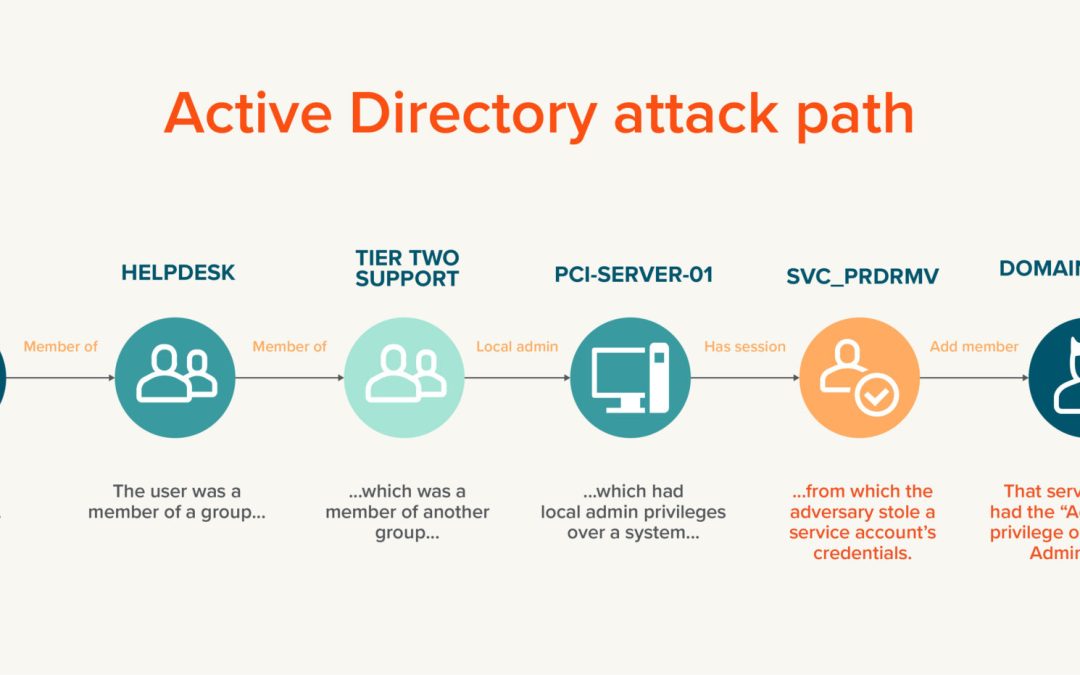
Attack paths are at the forefront of cybersecurity discussions today. But exactly what is an attack path? Why is Active Directory (AD) particularly vulnerable? And what can you do to protect your organization? This blog post covers all these questions and more. ...

Mar 21, 2023 | Articles, Articles
Helsinki, Finland – March 16, 2023 – The US federal government has shown significant interest in Quantum-Safe communications during 2022, most evidently through Quantum Cybersecurity Preparedness Act, which mandates all electronic communications to be...